Your Salesforce reports look clean until someone asks a simple question: why does pipeline in HubSpot differ from pipeline in Salesforce, and why do finance numbers in the ERP tell a third story?
That’s the everyday RevOps problem. Lead source lives in one system, campaign response in another, opportunity data in Salesforce, product or billing history somewhere else, and every team assumes their dashboard is the right one. The underlying issue usually isn’t reporting. It’s architecture. If the integration model is wrong, your attribution breaks, lifecycle stages drift, deduplication gets harder, and forecasting turns into reconciliation work.
A lot of teams searching for a salesforce connect app are mixing up two very different Salesforce frameworks. One handles secure access for external applications. The other surfaces external data inside Salesforce without copying it in. That distinction matters because the wrong choice creates technical debt fast. You either over-sync data that shouldn’t be stored in Salesforce, or you under-govern an app that has more access than anyone realised.
The RevOps Struggle with Siloed Data
A typical B2B stack isn’t small anymore. Salesforce Sales Cloud runs the CRM. HubSpot or Account Engagement handles parts of marketing automation. Sales engagement tools log activity. Enrichment tools like Clay and ZoomInfo feed account data. Finance or order history often stays in an ERP or a custom database. Every handoff introduces one more place where the truth can split.

When teams say they need “an integration”, they often mean different things:
- Marketing wants sync reliability. They need campaign members, lead status, scoring inputs, and attribution touchpoints to move cleanly between systems.
- Sales wants context in one screen. Reps don’t want to open three platforms to understand an account.
- RevOps wants governance. Admins need to know which app can access what, which user authorised it, and whether the setup will survive the next process change.
- Leadership wants one number. They need pipeline, conversion, and revenue reporting they can trust.
That’s why integration design isn’t just an admin task. It shapes reporting quality, CRM hygiene, compliance posture, and speed of execution across the GTM team.
Siloed data rarely starts as a technology failure. It starts when each team solves its own problem without a shared integration model.
In practice, there are two questions underneath almost every salesforce connect app conversation. First, do you need an external system to act on Salesforce through APIs? Second, do you need Salesforce users to see external data in place without storing it locally?
Those are different patterns. If your team hasn’t separated them yet, it’s worth grounding the conversation in a clearer view of data synchronisation before you buy another connector or approve another app.
Connected Apps vs Salesforce Connect The Core Distinction
The fastest way to understand this is to stop treating the names as interchangeable.
A Connected App is a keycard. It gives an external application a controlled way to enter your Salesforce org and do something through authentication and API access.
Salesforce Connect is a window. It lets Salesforce users look at data that still lives in another system, in real time, without importing that data into standard or custom Salesforce objects.
That’s the core distinction. One is about secure application access. The other is about data virtualisation.
The keycard model
When HubSpot, Salesloft, a custom app, or an internal service needs to call Salesforce APIs, it typically does that through a Connected App. You configure permissions, session behaviour, permitted users, and authentication settings. The app authenticates, gets the right level of access, and then creates, reads, updates, or queries data based on what it’s authorised to do.
This is the pattern you use when data has to move.
Typical examples include syncing form fills into leads, pushing sales activity into Salesforce, updating campaign membership, or letting middleware transform and write data across platforms.
The window model
Salesforce Connect works differently. It doesn’t focus on moving records into Salesforce first. Instead, it exposes external objects so users can work with outside data from within the Salesforce interface. The external system remains the system of record.
This is the pattern you use when people need visibility, but copying the data creates more problems than it solves.
That matters for ERP data, order history, subscription usage, support entitlement data, or large legacy datasets where freshness matters and storage duplication adds noise.
Salesforce Integration Frameworks at a Glance
| Criterion | Connected Apps (The 'Keycard') | Salesforce Connect (The 'Window') |
|---|---|---|
| Primary role | Secure external app access to Salesforce | Real-time access to external data inside Salesforce |
| Best for | API integrations and data movement | Data virtualisation and in-place visibility |
| Where data lives | Often copied, synced, or updated in Salesforce | Remains in the external source |
| User experience | Usually powers background syncs or app actions | Makes outside data appear in Salesforce UI |
| Control point | OAuth policies, users, scopes, sessions | External data source config, adapters, object mapping |
| Common RevOps example | HubSpot sync, sales engagement logging, custom workflow automation | Showing ERP order history on account or opportunity records |
| Main trade-off | Strong operational flexibility, but more governance needed | Less duplication, but depends on source performance and data model quality |
Where teams get this wrong
The confusion usually shows up in project scoping. A team asks for “Salesforce Connect” when what they really need is a Connected App for OAuth access. Or they push millions of external records into Salesforce because no one considered whether those records needed to live there.
That second mistake gets expensive. It also creates downstream reporting clutter, duplicate logic, and a lot of maintenance no one planned for. If you’re modernising old integrations or exposing legacy systems to Salesforce, this piece on Avoiding costly modernization pitfalls is useful because it frames the architectural decision before you commit to a pattern you’ll have to unwind later.
Choose the keycard when a system needs to do something in Salesforce. Choose the window when users need to see something from outside Salesforce.
Once that model is clear, the design conversations get much better. You stop asking which connector is easiest and start asking where the source of truth belongs, how fresh the data needs to be, and who should control access.
A Deep Dive into Salesforce Connected Apps
Most RevOps integrations rely on Connected Apps whether the team realises it or not. If a third-party platform needs to authenticate into Salesforce, call APIs, or support single sign-on, this is usually the framework doing the work behind the scenes.

Salesforce documents that Connected Apps form the backbone of API integrations using protocols like SAML, OAuth, and OpenID Connect. They’re installable across all editions and support policies for permitted users, session timeouts, and high-assurance sessions. Salesforce’s broader platform footprint also matters here. The company reported that Sales and Service clouds made up 48.25% of subscription revenue, including $7.5B Sales and $8.2B Services, as noted in the Salesforce connected app metadata documentation.
What a Connected App actually does
A Connected App defines how an outside application can authenticate and what happens once access is granted. In plain terms, it answers questions like these:
- Which protocol is being used?
- Which users can authorise or use the app?
- What level of session security is required?
- What scopes allow API access or token refresh?
- How long should the session last before re-authentication?
For RevOps, that’s not abstract platform plumbing. It affects whether your sync survives user turnover, whether your sales engagement platform can still log tasks, and whether a marketing tool can update lead and contact records without overreaching.
The settings that matter in real life
Admins often create a Connected App once and never revisit it. That’s a mistake. Several settings have direct operational consequences.
- OAuth scopes determine what the app can do. If an app only needs API access and token refresh, don’t give it wider access than necessary.
- Permitted users matters more than many teams expect. “Admin approved users are pre-authorized” is usually safer than letting any user self-authorise.
- Session policies affect risk and reliability. Tight settings improve control, but they can break background integrations if they’re too aggressive.
- High-assurance requirements make sense for sensitive use cases, but they should match the actual business process.
Where Connected Apps fit in a B2B stack
In a practical GTM environment, Connected Apps usually sit beneath workflows people talk about in business terms.
A few common examples:
HubSpot to Salesforce sync
HubSpot needs authenticated access to create or update leads, contacts, companies, and sometimes custom object mappings depending on the architecture.Sales engagement logging
Tools that write emails, calls, tasks, or meeting activity back to Salesforce need governed access that won’t disappear when an employee leaves.Custom lead routing or enrichment
Internal services may enrich records, standardise fields, or score hand-raisers before handing them to sales.Single sign-on
SAML or OpenID Connect can tie user authentication to broader identity management requirements.
Practical rule: if an external platform needs permission to read from or write to Salesforce, start by reviewing the Connected App design before you review the sync rules.
What works and what usually does not
What works is straightforward governance. One app, one purpose, tight scopes, deliberate permissioning, and clear ownership. The best setups also document which business process depends on that app, which objects it touches, and who signs off on changes.
What doesn’t work is treating every integration as a one-off exception. That’s how teams end up with legacy tokens, over-permissioned apps, and “temporary” settings that become permanent.
A Connected App is not the integration itself. It’s the trust framework around the integration. If that trust layer is weak, every workflow built on top of it is fragile.
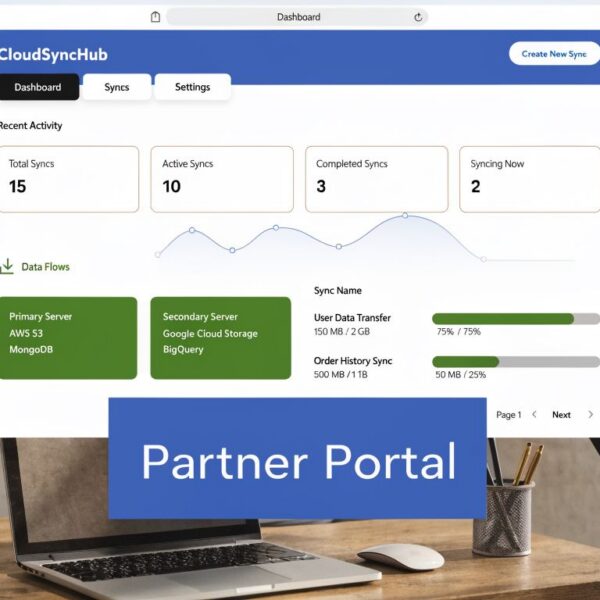
When to Use Salesforce Connect for RevOps
Salesforce Connect is the right answer when you need access to external data, but you don’t want to replicate that data into Salesforce just to make it visible.
That situation comes up more often than teams expect. Finance owns order history in an ERP. Product usage lives in a separate database. A service team tracks fulfilment outside CRM. Sales still needs the context, but copying all of it into Salesforce can make reporting messy and inflate storage unnecessarily.

The real strength of the window approach
Salesforce Connect uses external objects to surface data from another source. The data stays outside Salesforce, but users can interact with it through the Salesforce interface. According to the referenced overview, Salesforce Connect enables real-time integration of external data via external objects using OData 2.0/4.0 or custom Apex adapters, and Salesforce has reported 50-70% storage cost reduction in pilots. The same source also notes that this can help firms avoid unnecessary duplication and support compliance under CPRA, where penalties can reach $7,500 per violation in the cited context, as described in this Salesforce Connect summary.
For RevOps, that means you can show a rep what they need without turning Salesforce into a warehouse for every operational dataset.
Good fits for Salesforce Connect
This model tends to work well in a few specific scenarios:
- ERP and order data when sales needs current commercial history on the account record
- Large legacy datasets that are queried occasionally, but are too bulky to sync wholesale
- Regional or regulated data environments where duplicating customer data creates governance issues
- Operational reference data that helps decisions but doesn’t need to drive heavy automation inside Salesforce
Adapter choice changes the project
The adapter is not a small implementation detail. It determines how realistic the architecture is.
| Adapter type | Best use | RevOps implication |
|---|---|---|
| OData 2.0 or 4.0 | External systems that already expose REST-friendly data services | Faster path when the source is well-structured |
| Custom Apex adapter | Proprietary or non-OData APIs | More flexibility, but more build and maintenance overhead |
| Salesforce-to-Salesforce adapter | Multi-org visibility needs | Useful when teams run separate Salesforce environments |
Trade-offs teams should acknowledge early
Salesforce Connect is not a shortcut for every integration need. It’s best when people need visibility, not heavy writeback automation. If sales needs to trigger workflows, ownership logic, or lifecycle changes based on external data, you may still need a separate integration layer.
It also depends on the quality and responsiveness of the source system. If the external system is poorly structured, slow, or inconsistent, Salesforce Connect will surface those weaknesses instead of hiding them.
Use Salesforce Connect when copying the data would create more operational burden than business value.
For pipeline visibility, account context, and cross-system access, it’s often a smarter design than another sync job.
Implementation Best Practices for Secure Integrations
Most integration failures aren’t caused by missing features. They’re caused by bad security decisions dressed up as convenience.
Teams share one integration user across several tools. They grant broad scopes because narrowing them takes time. They leave old apps in place because no one wants to test what breaks. Then an audit starts, or a sync fails, or a suspicious login appears, and everyone discovers how little control they actually had.

The shared user shortcut is riskier than it looks
A lot of admins inherit the idea that one low-privilege integration user is cleaner and easier to manage. In reality, that can create permission sprawl across apps that were never meant to share a trust boundary.
A cited security analysis presents a strong counterpoint: a 2025 CA Data Privacy study found that 72% of 320 Salesforce breaches exploited shared users where cumulative permissions exceeded scopes, and the same source cites a Deloitte report claiming dedicated users per app can reduce breach probability by 58%, based on the summary in this connected app security risks analysis.
That doesn’t mean every small team needs a complex identity programme overnight. It does mean the “single integration user for everything” habit deserves more scrutiny than it gets.
Security controls that actually help
A secure salesforce connect app setup is less about adding friction everywhere and more about being deliberate.
- Separate users by integration purpose. Give HubSpot, a sales engagement tool, and internal middleware their own identities where possible.
- Keep OAuth scopes narrow. If the app doesn’t need broad access, don’t grant it.
- Use admin-approved access patterns. That prevents ad hoc user authorisation from subtly widening your exposure.
- Review usage regularly. Connected Apps OAuth Usage should be part of operational hygiene, not just incident response.
- Document app ownership. Every app should have a business owner and a technical owner.
For teams mapping designs before implementation, this NineArchs LLC integration guide is useful because it frames pattern choice around architecture rather than just vendor setup.
Rotation and audit discipline
Secrets and consumer keys shouldn’t stay untouched until there’s a problem. Salesforce documents a staged approach to rotating consumer details, and admins can manage that from App Manager through consumer detail management. The same guidance notes there can be up to 10 minutes of intermittent instability after applying the change, which matters when the integration supports active GTM workflows. That’s why rotations should be scheduled, tested, and communicated rather than done casually in production.
There’s also a compliance angle. If your team handles customer data across multiple systems, your integration posture needs to align with broader API governance and privacy obligations. This guide to application programming interface security is a useful companion read because it brings the security conversation back to practical controls, not abstract policy.
A healthy integration estate is boring on purpose. Known apps. Known owners. Narrow access. Predictable rotation. Clear audit trails.
What to stop doing
A few habits create avoidable risk:
- Letting users self-authorise tools without review
- Keeping legacy apps because “nothing’s broken”
- Reusing credentials across unrelated integrations
- Treating audit logs as optional
- Waiting for a vendor migration or security change before cleaning up access
Security-first integration design doesn’t slow RevOps down. It prevents hidden instability from showing up in the middle of a quarter when pipeline reporting and routing matter most.
Troubleshooting Common Integration Headaches
When an integration fails, the visible symptom is rarely the root cause. A sync stops. Users lose access. Records stop updating. Someone blames Salesforce, then blames the other platform, and hours disappear before anyone checks the actual auth path.
The faster approach is to treat troubleshooting as pattern recognition. Start with the symptom, identify the likely failure point, then verify the specific setup element that controls it.
Symptom and cause map
| Symptom | Likely cause | First check |
|---|---|---|
| User is not pre-authorized for this consumer | Connected App policy requires admin approval, but the user lacks the right permission set or assignment | Permitted Users setting and assigned permission sets |
| Auth worked before, then failed after personnel changes | The integration was tied to a deactivated or changed user context | Integration user status and recent admin changes |
| Intermittent failures after secret rotation | Consumer detail changes are still propagating | Rotation timing and whether the new credentials were applied too early |
| Unexpected access prompts or blocked use | App authorisation policy no longer matches current governance | Connected App usage and approval model |
| Slow downstream sync behaviour | Excessive API activity, poor sequencing, or source-side delay | API usage patterns and app call behaviour |
What to check in Salesforce first
Don’t start in the external app. Start in Salesforce because the auth and policy controls are often the source of the issue.
Review Connected App policies
Check permitted users, session settings, and whether the access model changed during a cleanup or release cycle.Confirm the integration user
Verify the app still points to the right user identity and that the user hasn’t been deactivated, permissioned down, or moved into a profile that lost required object access.Inspect audit and identity activity
Salesforce Help notes that identity reporting can show fields including Username, User ID, Identity Used, App: Connected App Name, Timestamp, User Type, and SSO Type across all-time reporting. That’s useful when you need to trace whether the app attempted authentication and under which identity context.
When an integration breaks, check policy drift before you check payload mapping. Access control failures often look like data issues at first.
Secret rotation is a common self-inflicted outage
Consumer key and secret rotation is good practice, but it creates risk if the team changes credentials without a handover plan. Salesforce’s documented process allows staged updates, but there can be up to 10 minutes of intermittent instability after the change is applied, according to the earlier Salesforce Help guidance.
That means a careful rotation plan should include:
- A clear maintenance window so ops teams know a short disruption is possible
- A dependency list of every system using that Connected App
- Credential update sequencing so external tools are ready before the final apply step
- Post-change validation in the live business workflow, not just in the app console
A practical triage order
When a salesforce connect app issue lands in Slack, this order usually saves time:
- Check access and policy changes first
- Validate the user tied to the integration
- Review recent credential updates
- Look at usage and identity logs
- Only then inspect field mapping or payload logic
Many “data sync” incidents are really authentication or permission incidents wearing a data symptom. If the trust layer is unstable, everything above it becomes unreliable.
Optimising Your GTM Stack with the Right Strategy
The useful decision is simpler than the product names make it sound.
Use Connected Apps when an external tool needs a secure way to authenticate into Salesforce and perform actions through APIs. Use Salesforce Connect when Salesforce users need access to external data in real time without importing and maintaining that data inside the CRM.
That choice affects more than integration diagrams. It shapes reporting trust, process reliability, and how much operational drag your team carries quarter after quarter.
A practical decision lens
Ask these questions before you build:
Does the external system need to read or write Salesforce data?
That points toward a Connected App pattern.Do users just need to view external data inside Salesforce?
That points toward Salesforce Connect.Is Salesforce meant to become the system of record for this dataset?
If not, don’t force it there.Will this dataset drive automation, assignment, or lifecycle logic?
If yes, a virtualised view alone may not be enough.
When a team can handle it internally
An in-house team can usually manage the design if the environment is relatively clean, app ownership is clear, and the project affects a limited number of systems. The same applies if your admins already maintain permission sets, know where data ownership sits, and can test integrations without guessing.
A good internal team also knows when to say no. Not every field needs syncing. Not every record needs to live in Salesforce. Not every vendor default should be accepted.
When expert help becomes worth it
Outside support starts making sense when any of these are true:
| Situation | Why it gets harder |
|---|---|
| Multiple systems influence revenue reporting | Source-of-truth conflicts become expensive |
| Legacy integrations exist without documentation | Cleanup risks breaking live processes |
| Compliance or privacy review is involved | Access design needs tighter governance |
| Salesforce and HubSpot both drive GTM workflows | Ownership and sync logic often overlap |
| Teams want scale without adding admin burden | Architecture quality matters more than quick fixes |
If your current estate already feels tangled, a platform integration review is usually the best starting point. This guide to platform integration strategy is useful because it frames integration as an operating model, not just a connector decision.
The main point is this: don’t choose a salesforce connect app pattern because the names sound close or a vendor demo made it look easy. Choose it based on where the data should live, who needs access, what actions must happen, and how much governance the business needs.
If your team is trying to untangle Salesforce, HubSpot, and the rest of your GTM stack, MarTech Do can help you choose the right integration pattern, audit existing app risk, and build a cleaner RevOps architecture that supports reliable reporting, stronger data hygiene, and better execution across marketing, sales, and customer teams.